Healthcare Workforce Trends: Staffing Ratios and Job Satisfaction
In the world of healthcare, both professionals and patients are on the brink of a revolution, driven by rapid technological advancements and groundbreaking innovations.
These changes are not only reshaping the way care is delivered but are also significantly altering the landscape of employment within the industry
As new technologies emerge, they bring with them a burgeoning demand for a diverse range of skills and expertise, creating both challenges and opportunities for healthcare facilities and workers alike.
This evolving scenario calls for a deeper understanding of how staffing trends and job satisfaction are intertwined with the future of healthcare.
The Crucial Role of Staffing Ratios
Staffing ratios—the number of healthcare providers to patients—remain a fundamental metric in healthcare management.
These ratios are critical because they directly impact the quality of patient care and the work environment for staff. Optimal staffing ensures that patients receive the attention they require for their health needs, which in turn facilitates better recovery outcomes.
In many healthcare settings, especially those experiencing staffing shortages, the workload can become overwhelming, leading to increased stress and burnout among healthcare workers. This not only affects their health and job satisfaction but also the quality of care provided to patients.
For instance, research indicates that hospitals with favorable nurse-to-patient ratios see significantly lower readmission rates and better patient outcomes compared to those with less favorable staffing.
A study from Science Direct found that increasing the nurse staffing ratio by just one patient per nurse could reduce hospital readmissions by up to 5%.
Trends Influencing Staffing Ratios
Several trends currently influence staffing ratios in healthcare. Such as:
Aging Population
The growing number of elderly individuals is escalating the demand for healthcare services. This demographic shift requires more hands on deck, particularly in specialties dealing with chronic and age-related conditions.
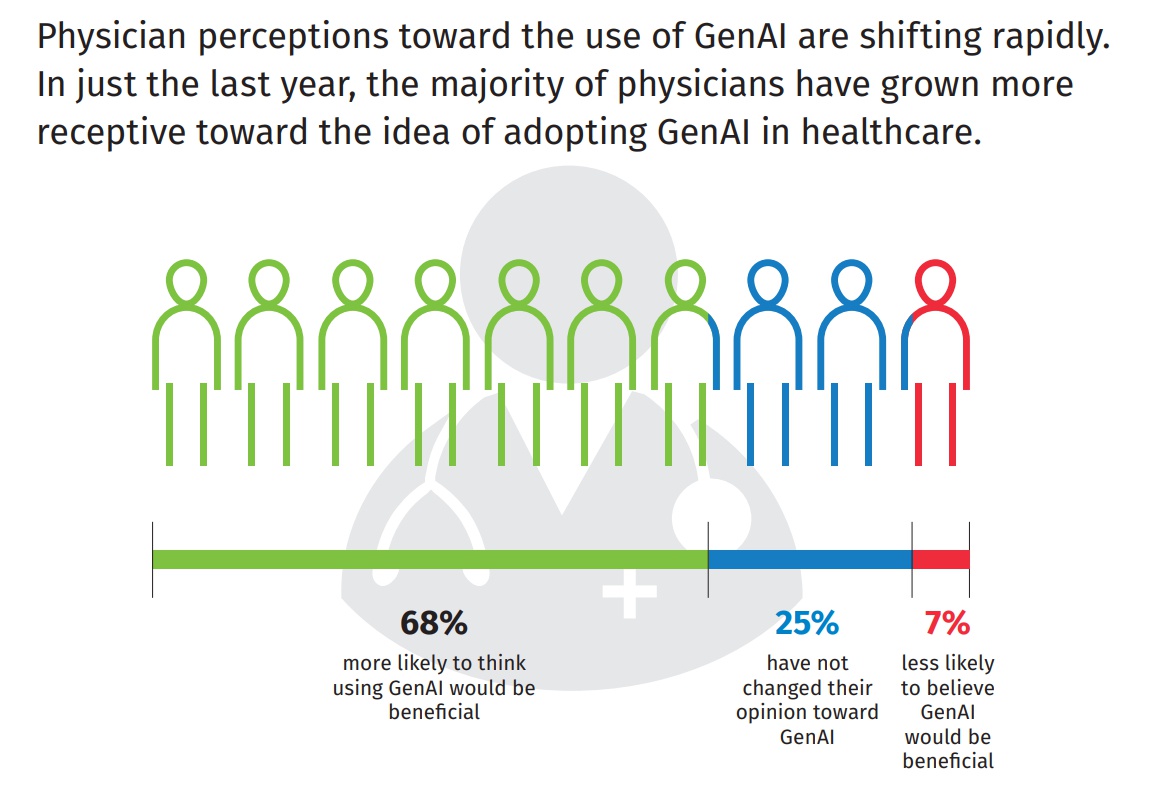
Technological Advancements
While technology promises greater efficiency, it also demands new skills and continuous learning from healthcare professionals.
Technologies such as telemedicine, robotic surgery, and AI-driven diagnostics require specialized training, thus impacting staffing as facilities must consider both numbers and capabilities.
Regulatory Requirements
Different regions have responded to staffing challenges by implementing regulatory measures. For example, certain U.S. states have enacted laws specifying minimum nurse-to-patient ratios in an effort to standardize care quality across facilities.
Job Satisfaction Among Healthcare Workers
Job satisfaction in the healthcare sector is closely linked to staffing levels.
Adequate staffing not only reduces the pressure on existing staff but also improves their job satisfaction by creating a less stressful and more supportive working environment.
Research by Butterworth et al. (1999) highlighted the significant stress levels British nurses face, with occupational stress on the rise.
It was reported that 40% of hospital nurses experienced burnout, and one in five considered leaving their jobs within the following year. This is because they endure considerable stress due to long working hours, a wide range of tasks, and complex relationships with patients, their families, and co-workers.
Addressing Challenges through Strategic Approaches
Innovative Recruitment and Retention Strategies
Attracting and retaining skilled healthcare professionals is more critical than ever. Innovative strategies such as offering competitive salaries, flexible work schedules, and opportunities for professional development are vital.
Additionally, creating a supportive work environment that values each team member’s contribution can improve retention rates.
Leveraging Technology to Optimize Workforce Management
Healthcare facilities can use advanced scheduling software to optimize staff allocation based on patient acuity and predicted admission rates. These tools can help manage workload distribution more effectively, ensuring that no single team or individual is overwhelmed.
Enhancing Training and Education
Continued education and training programs are essential for keeping staff at the forefront of the latest medical advancements. Investing in education not only equips healthcare professionals with the necessary skills but also contributes to job satisfaction as they feel more competent and valued. Incorporating provider credentialing services into these training programs ensures that all credentials are up to date, further enhancing staff competency and compliance.
Fostering a Positive Work Culture
A positive work environment that promotes team collaboration, respects personal time, and recognizes hard work is crucial for job satisfaction. Regular feedback sessions and team-building activities can enhance the work culture significantly.
Embracing Outsourcing
Outsourcing non-core activities such as revenue cycle management to a medical billing company significantly alleviates the workload on healthcare staff.
By delegating tasks such as administrative duties, billing, and even certain clinical support services to external providers, facilities can allow healthcare professionals to focus more on patient care.
This approach not only streamlines operations but also can enhance job satisfaction by reducing the stress and burnout associated with juggling multiple responsibilities.
Conclusion
As the healthcare industry continues to evolve under the influence of demographic shifts, technological advancements, and regulatory changes, understanding and adapting to the trends in staffing ratios and job satisfaction becomes imperative.
Healthcare providers and facility owners must stay informed and proactive in addressing these trends to ensure that they not only meet the standards of care but also maintain a satisfied and motivated workforce.
Through strategic planning and thoughtful leadership, the challenges presented by these trends can be transformed into opportunities for growth and improvement.